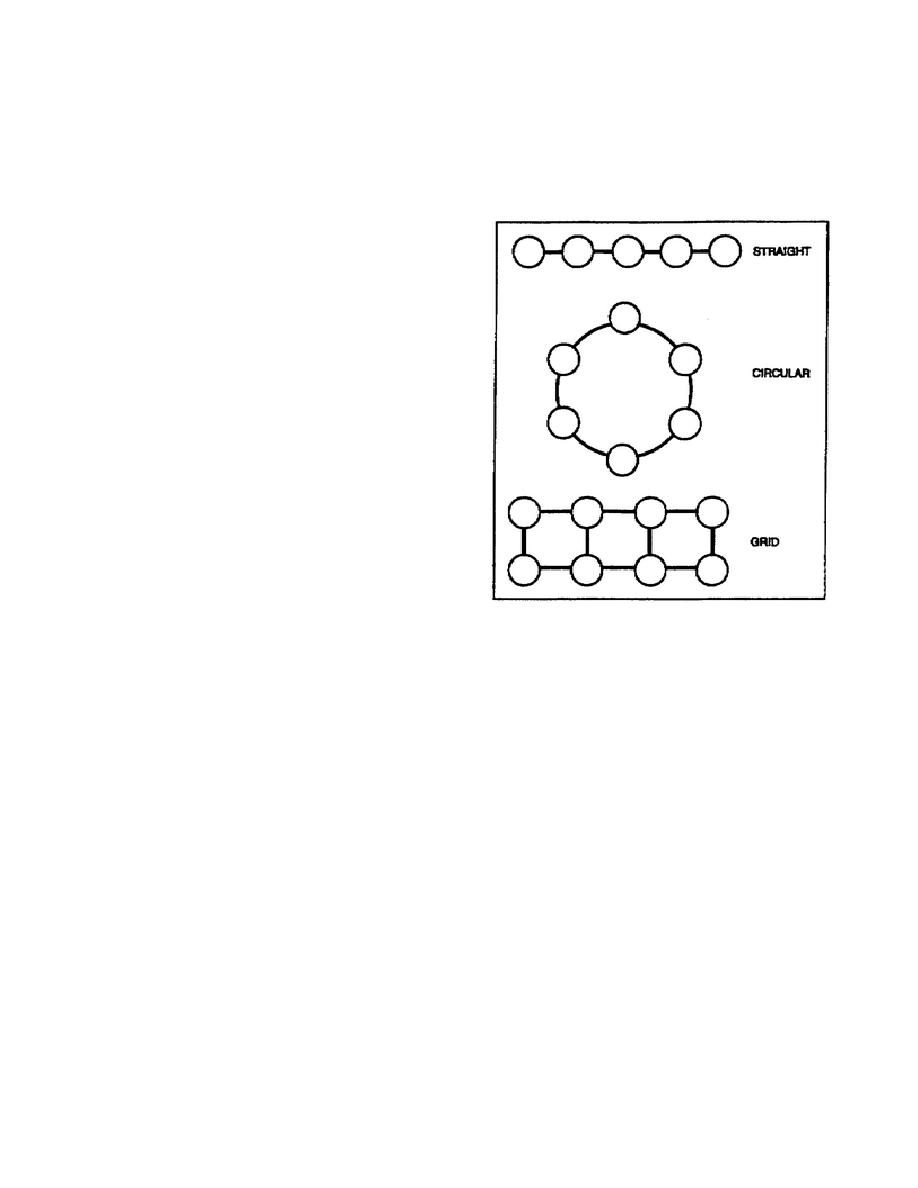
(2) In designing communications systems, we must establish alternate
routes of communications. With enough routes, the loss of one or more will
not seriously degrade the overall system. Figure 3 shows the three possible
routing configurations.
The straight-line method provides no alternate
routes. The circular method allows one alternate route of communications.
The grid method allows as many alternate routes as can be planned
practically.
b.
Enemy forces can extract
vital information from friendly
communications patterns.
Thus,
friendly forces should not have any
sort of communications pattern.
Traffic
(keeping
transmission
traffic
fairly
constant) should also be practiced.
The frequency of messages being
sent can tell enemy analysts what
type of mission friendly forces are
likely
planning
or
doing.
Introducing false messages on a
random basis can prevent an enemy
from detecting operations. This is
especially true during periods when
actual message traffic decreases.
Properly using and enforcing signal
operation instructions (SOI) can
help
eliminate
communications
patterns.
Whatever method is used
needs to be carefully planned and
fully integrated into the unit's
OPLANs and OPORDs.
Consider the
Figure 4-3. Deployment
type of equipment used and its
configurations.
location,
power,
and
operating
methods when planning ECCM. To make
communications more secure, use:
(1) Low power until you must use high power.
(2) Frequency hopping to deny interception from enemy forces.
patterns.
(4) Spread spectrum techniques to suppress interference and provide
multiple access for other users.
c. The
replacement
category
involves
establishing
alternate
communications routes. These must be planned and exercised before engaging
an enemy. This can stop them from setting up a database on primary friendly
communications.
It can also help to maintain the primary communication
means available to the tactical commander.
Replacement actions must be
carefully planned, coordinated, and integrated into the units OPLAN or
OPORD.
SS0135
4-4



 Previous Page
Previous Page
