c. ECCM are defensive measures used to protect friendly command,
is closely related to signal security (SIGSEC). The main difference
between the two is the type of information being protected from the
enemy. ECCM protects friendly emitters from enemy EW assets. SIGSEC
protects the information friendly forces transmit.
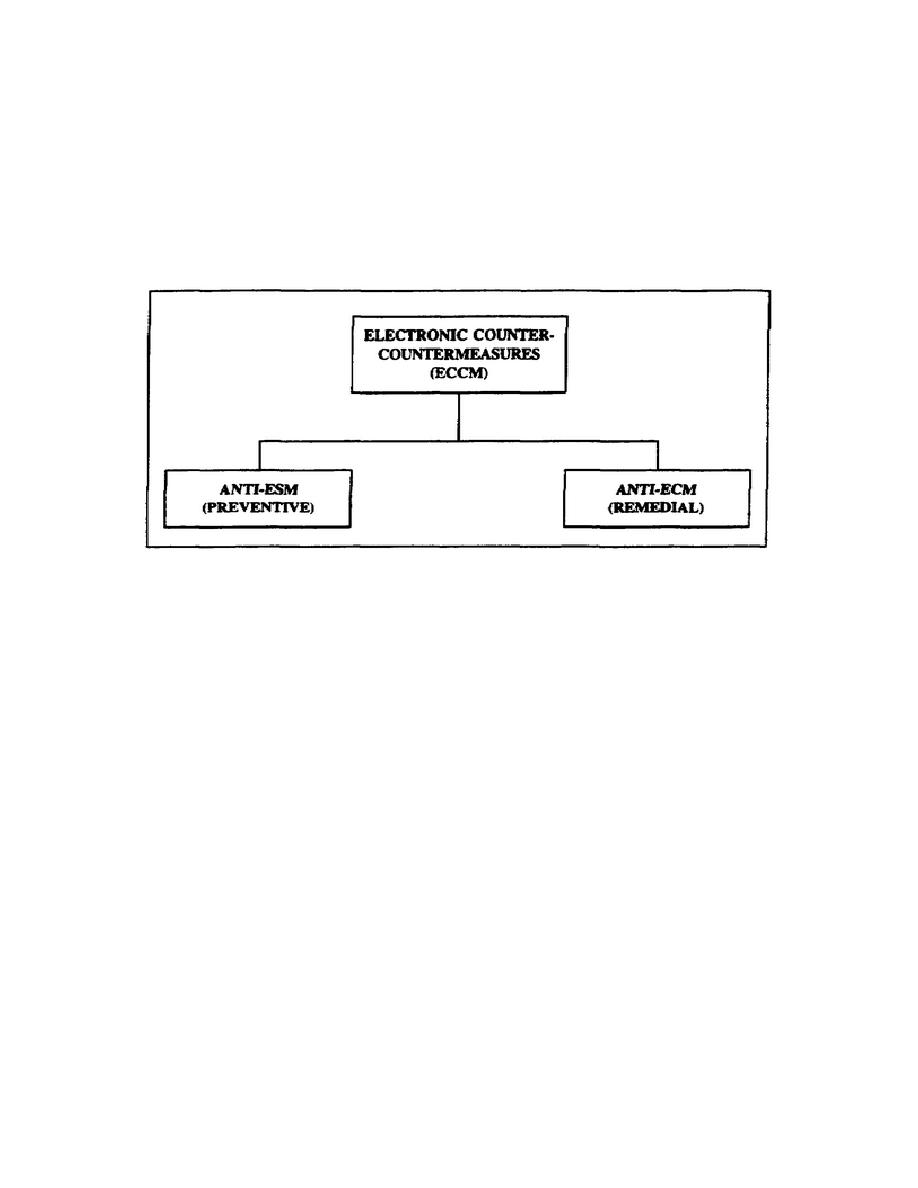
ECCM allows
friendly forces the continual use of the electronic spectrum by anti-
ESM (preventive) and anti-ECM (remedial) activities (Figure 1-3).
ECCM falls under the direction of the G3.
Figure 1-3.
ECCM components.
(1) Anti-ESM are actions taken to deny the enemy access to
friendly force's electromagnetic transmissions.
This is done by
avoiding the enemy force's EW operations. To deny an enemy access to
friendly electronic assets, several actions may be taken. An example
is terrain masking, where a friendly radio station is placed, so an
obstacle (such as a hill) is between it and the enemy.
A second
example is avoidance (using a directional antenna). A third example
is emission control (operating at the lowest power needed, turning on
the transmitter only when needed, and using random scheduling for
communicating, if possible).
(2) Anti-ECM are used against jamming, but cannot be used
against deception or ESM.
Anti-ECM involve actions taken after
discovering that the enemy is using EW against friendly forces.
Effective anti-ECM methods are determining the cause of interference,
recognizing the difference between jamming and natural interference,
changing frequencies, or shutting down communications and switching
to alternate frequencies.
SS0134
1-8



 Previous Page
Previous Page
